Updates: Prod, Partners & Scale
It has been a couple of weeks since our last update, but we're excited to share that our core data pipeline, ancillary processes and analytic engines have been operating with near perfect stability for several weeks, requiring us to horizontally scale on-prem infrastructure and begin implementing the cloud infra designed during Dendrite's inception. As you can imagine, the compute and hot cache storage requirements for this project are absolutely massive: Not only are we extracting a huge amount of data from the dark, deep and surface webs, but we’re also enriching and transforming it, then correlating many hundreds of data points from each record to other records and resources where appropriate.
What our plans mean for the end user is more timely and relevant data, in that we're focused primarily on the resources we're able to allocate to our core data pipelines and engines. This means more rapid refresh rates for the records (users, malicious infrastructure, and online resources) you have set alerts for and new record creation for the same, getting us one step closer to threat, campaign and event prediction.
Prod: Building on the Cloud
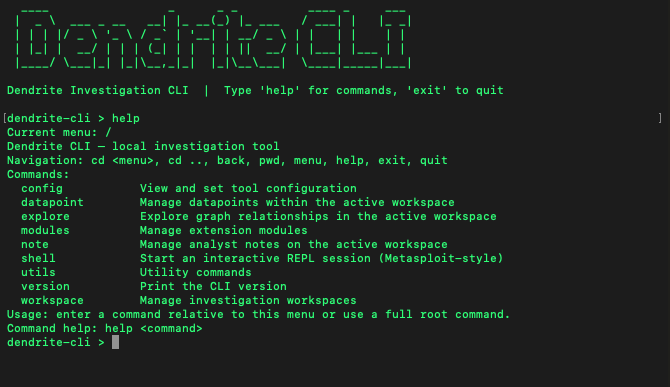
Over next few weeks, we'll also be deploying the public cloud infrastructure, which is primarily intended to operate as user authentication, serve layer and hot cache for the Unified Web Platform, API access and CLI Utility. Once complete and our datasets are uploaded, we will finally be at the point where we can offer access via the latter two methods - which will be an exciting day for the company.
Startup screen for the dendrite CLI Utility.
The Unified Web Platform is also close to completing its early-release development phase, and I have to say: I have a new found level of respect for webapp developers and the harsh realities expressed through countless meme’s on X. My programming and architecture experience is mainly with data pipelines, security tools and complex back end programs, so this has been a new experience for me – and not as fun as it sounds. Though I think that the early-release version of the UWP will work well for most people’s needs, I can guarantee that I’ll be celebrating the hire of our webapp developers harder than anyone else.
A sneak peek at the web portal, where users will be able to explore Dendrite and 3rd party data sources in graphical view, participate in forums, encrypted chat, manage org users & API keys.
— Dendrite (@dendrite_tech) May 7, 2026
Video walkthroughs by @TG01_Actual are in the works and for release soon. pic.twitter.com/4WqBtbsCxU
Unified Web Platform: Beta Testers
Also on the topic of the UWP, we will be looking for beta testers from our trusted friends and followers, so send us a message if you would like to be included it this group. Testers will be able to query a scaled (demo) version of the complete databases, explore data in graph view, start threads and subs on the forums, use the encrypted chat and more.
Though access will close within a specific window, we will migrate your account, message & forum history to your new account when beta testers are part of a paid enterprise or individual subscriber plan.
On Seeking Partners
This has been an interesting internal dilemma since we first passed through our POC phases: Do we seek partners and if so, what type, how many. how do we work with them, etc. We're always happy to have discussions (and I don't believe that we've turned down one yet) with potential VC investors, corporate sponsors or partners. At the moment however, our main focus will likely be on technical, product and GTM partnerships - which we believe is true to our founding goals of building fusion data layers with existing security, detection and analysis workloads.
This said, our DM's are open and we'd love to hear from anyone who has an interest in working with us.
One group of partners we would like to begin working with in the immediate future are orgs and foundations working to prevent human trafficking and the online distribution of CSAM. Given Void Runner’s ability to characterize and index the .onion and I2P versions of the dark web (approaching 7 million records averaging over 250 data points each), identify it's infrastructure and often ascertain user identity; we believe that we can greatly enhance investigation workflows this category. With this in mind, we're planning to donate scoped Dendrite access to groups in this fight, and would love to start discussions on how to better align our offering with your needs - and I’m even happy to build a suite of capabilities unique to these needs if necessary. If you are reading this an know of someone who might be interested, please reach out.
Scaling the Team
If all goes well over the coming months and mid summer, we'll be looking to immediately expand the Dendrite team and roster of approved part-time contractors. At this time, we're planning to include the following:
Developers - Web Platform and core software development. These team members will take ownership of well defined roadmap capabilities and be charged with the continue evolution of Dendrite capabilities.
Security & Infra Engineers - Tasked to help build out a lot of the next generation of infrastructure based on existing plans, and secure existing infrastructure for both Dendrite and the end users.
Sales & CRM - Historically I've treated this as one and the same, where the person with the rapport with the client manages all communications and the relationship with clients. This role will focus mainly enterprise account development and management.
Cloud & Platform Admin - This role will manage cloud services, moderate forums and jump in with the team on other projects in alignment with their professional goals. I generally view admin's as an entry level role, which means that we'll be selecting candidates based on ethic.
All of these roles have complete job descriptions which will be posted to our X.com and LinkedIn page at the same time. Be sure to follow for updates on these as they become available.
Closing Thoughts
As the development and testing of our pre-launch capabilities approaches completion, we’re going to make an effort to be much more active here and on our X and LinkedIn accounts. DM’s are always open and I hope that everyone will feel free to reach out if they have any questions or would like to join in the conversation and testing.